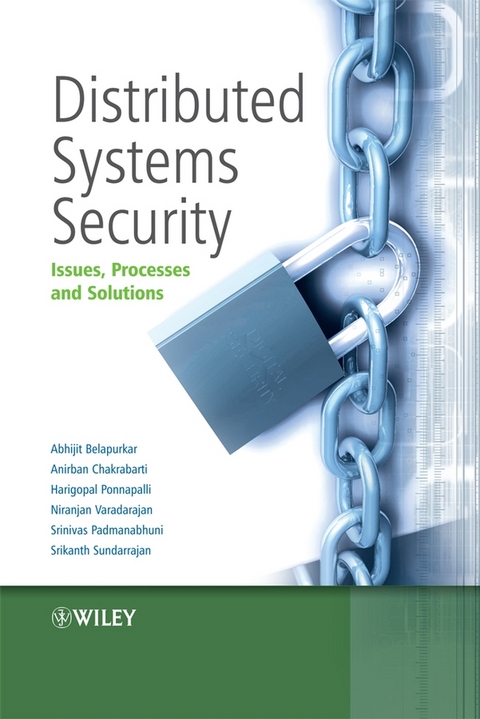
Distributed Systems Security (eBook)
334 Seiten
John Wiley & Sons (Verlag)
978-0-470-75177-0 (ISBN)
systems.
Security is one of the leading concerns in developing dependable
distributed systems of today, since the integration of different
components in a distributed manner creates new security problems
and issues. Service oriented architectures, the Web, grid computing
and virtualization - form the backbone of today's
distributed systems. A lens to security issues in distributed
systems is best provided via deeper exploration of security
concerns and solutions in these technologies.
Distributed Systems Security provides a holistic insight
into current security issues, processes, and solutions, and maps
out future directions in the context of today's distributed
systems. This insight is elucidated by modeling of modern day
distributed systems using a four-tier logical model -host
layer, infrastructure layer, application layer, and service layer
(bottom to top). The authors provide an in-depth coverage of
security threats and issues across these tiers. Additionally the
authors describe the approaches required for efficient security
engineering, alongside exploring how existing solutions can be
leveraged or enhanced to proactively meet the dynamic needs of
security for the next-generation distributed systems. The practical
issues thereof are reinforced via practical case studies.
Distributed Systems Security:
* Presents an overview of distributed systems security issues,
including threats, trends, standards and solutions.
* Discusses threats and vulnerabilities in different layers
namely the host, infrastructure, application, and service layer to
provide a holistic and practical, contemporary view of enterprise
architectures.
* Provides practical insights into developing current-day
distributed systems security using realistic case studies.
This book will be of invaluable interest to software engineers,
developers, network professionals and technical/enterprise
architects working in the field of distributed systems security.
Managers and CIOs, researchers and advanced students will also find
this book insightful.
Anirban Chakrabarti holds a PhD degree from the Department of Electrical and Computer Engineering, Iowa State University in Dec. 2003. Currently he works as a Senior Research Associate in the Grid Computing Focus Group in Software Engineering Technology Labs (SETLABS) of Infosys Technologies, India. In Infosys he is working on the virtualization techniques in the Grid Computing area. In Grid computing his main interests lie in security, manageability, workflow management, and application engineering issues. He is also interested in research in the areas of Internet infrastructure encompassing security, routing and multicasting. Dr. Srinivas Padmanabhuni is a Principal Researcher at Software Engineering and Technology Labs (SETLabs) in Infosys Technologies Limited, Bangalore, India. He heads the Web Services and SOA centre of excellence in SETLabs at Infosys. Dr. Srinivas specializes in Enterprise Security, Web services, Service Oriented Architecture and Grid technologies alongside pursuing interests in semantic web, autonomic computing, recovery oriented computing, intelligent agents, and enterprise architecture. He is on editorial board of international journals, and has served on program committees for several international conferences and workshops including ICWS (International Conference of Web Services), PricAI (Pacific Rim International Conference on AI), NWeSP (International Conferenceon Next Generation Web Services Practices).
Chapter 1: Introduction
1.1 Background
1.2 Distributed Systems.
1.3 Distributed Systems Security.
1.4 About the Book.
Chapter 2: Security Engineering.
2.1 Introduction.
2.2 Secure Development Life Cycle Processes - An
Overview.
2.3 A Typical Security Engineering Process.
2.4 Important Security Engineering Guidelines and Resources.
2.5 Conclusion.
Chapter 3. Common Security Issues and Technologies.
3.1 Security Issues.
3.2 Common Security Techniques.
3.3 Summary.
Chapter 4 - Host level Threats and
Vulnerabilities.
4.1 Background.
4.2 Malware.
4.3 Eavesdropping.
4.4 Job faults.
4.5 Resource starvation.
4.6 Overflow.
4.7 Privilege escalation.
4.8 Injection attacks.
4.9 Conclusion.
Chapter 5 - Infrastructure Level Threats &
Vulnerabilities.
5.1 Introduction.
5.2 Network Level Threats and Vulnerabilities.
5.3 Grid Computing Threats and Vulnerabilities.
5.4 Storage Threats and Vulnerabilities.
Chapter 6: Application Level Vulnerabilities and
Attacks.
6.1 Introduction.
6.2 Application Layer Vulnerabilities.
6.3 Conclusion.
Chapter 7 - Service Level Issues, Threats and
Vulnerabilities.
7.1 Introduction.
7.2 SOA and Role of Standards.
7.3 Service Level Security Requirements.
7.4 Service Level Threats and Vulnerabilities.
7.5 Service Level Attacks.
7.6 Services Threat Profile.
7.7 Conclusions.
Chapter 8: Host level Solutions.
8.1 Background.
8.2 Sandboxing.
8.3 Virtualization.
8.4 Resource Management
8.5 Proof carrying code.
8.6 Memory firewall
8.7 Anti malware.
8.8 Conclusions.
Chapter 9 - Infrastructure Level Solutions
9.1 Introduction.
9.2 Network Level Solutions.
9.3 Grid Level Solutions.
9.4 Storage Level Solutions.
Chapter 10: Application Level Solutions.
10.1 Introduction.
10.2 Application Level Security Solutions.
10.3 Conclusion.
Chapter 11 - Service Level Solutions.
11.1 Introduction.
11.2 Services Security Policy.
11.3 SOA Security standards stack.
11.4 Standards in Depth.
11.5 Deployment Architectures for SOA Security.
11.6 Managing Service Level Threats.
11.7 Service Threat Solution Mapping.
11.8 XML Firewall Configuration-Threat Mapping.
11.9 Conclusions.
Chapter 12 - Case Study - Compliance in Financial
Services.
12.1 Introduction.
12.2 SOX compliance.
12.3 SOX Security Solutions.
12.4 Multi-level policy driven solution architecture.
12.5 Conclusions.
Chapter 13 - Case Study of Grid.
13.1 Background.
13.2 Financial Application.
13.3 Security Requirements Analysis.
13.4 Final Security Architecture.
Chapter 14: Future directions and Conclusions.
14.1 Future directions.
14.2 Conclusions.
| Erscheint lt. Verlag | 11.2.2009 |
|---|---|
| Sprache | englisch |
| Themenwelt | Informatik ► Theorie / Studium ► Kryptologie |
| Technik ► Elektrotechnik / Energietechnik | |
| Technik ► Nachrichtentechnik | |
| Schlagworte | Communication System Security • Computer Science • Computersicherheit • Electrical & Electronics Engineering • Elektrotechnik u. Elektronik • Informatik • Networking • Netzwerke • Sicherheit in Kommunikationssystemen |
| ISBN-10 | 0-470-75177-0 / 0470751770 |
| ISBN-13 | 978-0-470-75177-0 / 9780470751770 |
| Haben Sie eine Frage zum Produkt? |
Größe: 2,1 MB
Kopierschutz: Adobe-DRM
Adobe-DRM ist ein Kopierschutz, der das eBook vor Mißbrauch schützen soll. Dabei wird das eBook bereits beim Download auf Ihre persönliche Adobe-ID autorisiert. Lesen können Sie das eBook dann nur auf den Geräten, welche ebenfalls auf Ihre Adobe-ID registriert sind.
Details zum Adobe-DRM
Dateiformat: PDF (Portable Document Format)
Mit einem festen Seitenlayout eignet sich die PDF besonders für Fachbücher mit Spalten, Tabellen und Abbildungen. Eine PDF kann auf fast allen Geräten angezeigt werden, ist aber für kleine Displays (Smartphone, eReader) nur eingeschränkt geeignet.
Systemvoraussetzungen:
PC/Mac: Mit einem PC oder Mac können Sie dieses eBook lesen. Sie benötigen eine
eReader: Dieses eBook kann mit (fast) allen eBook-Readern gelesen werden. Mit dem amazon-Kindle ist es aber nicht kompatibel.
Smartphone/Tablet: Egal ob Apple oder Android, dieses eBook können Sie lesen. Sie benötigen eine
Geräteliste und zusätzliche Hinweise
Buying eBooks from abroad
For tax law reasons we can sell eBooks just within Germany and Switzerland. Regrettably we cannot fulfill eBook-orders from other countries.
aus dem Bereich