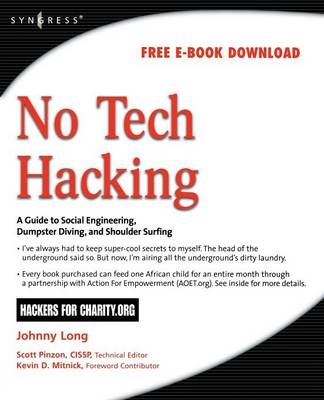
No Tech Hacking
Syngress Media,U.S. (Verlag)
978-1-59749-215-7 (ISBN)
Johnny Long's last book sold 12,000 units worldwide. Kevin Mitnick's last book sold 40,000 units in North America.
As the cliché goes, information is power. In this age of technology, an increasing majority of the world's information is stored electronically. It makes sense then that we rely on high-tech electronic protection systems to guard that information. As professional hackers, Johnny Long and Kevin Mitnick get paid to uncover weaknesses in those systems and exploit them. Whether breaking into buildings or slipping past industrial-grade firewalls, their goal has always been the same: extract the information using any means necessary. After hundreds of jobs, they have discovered the secrets to bypassing every conceivable high-tech security system. This book reveals those secrets; as the title suggests, it has nothing to do with high technology.
Johnny Long is a Christian by grace, a professional hacker by trade, a pirate by blood, a ninja in training, a security researcher and author. He can be found lurking at his website (http://johnny.ihackstuff.com). He is the founder of Hackers For Charity(http://ihackcharities.org), an organization that provides hackers with job experience while leveraging their skills for charities that need those skills. Kevin Mitnick (Technical Editor) is the most famous computer hacker in the world. Since his first arrest in 1981, at age 17, he has spent nearly half his adult life either in prison or as a fugitive. He has been the subject of three books and his alleged 1982 hack into NORAD inspired the movie War Games. Since his plea-bargain release in 2000, he says he has reformed and is devoting his talents to helping computer security.
1: Reading People
2: Social Engineering
3: Shoulder Surfing
4: Dumpster Diving
5: Physical Security
6: Death of a Road Warrior
7: Google and P2P Hacking
8: Anatomy of a Break-In
| Mitarbeit |
Herausgeber (Serie): Kevin D. Mitnick |
|---|---|
| Verlagsort | Rockland, MA |
| Sprache | englisch |
| Maße | 191 x 235 mm |
| Gewicht | 640 g |
| Themenwelt | Literatur ► Biografien / Erfahrungsberichte |
| Informatik ► Netzwerke ► Sicherheit / Firewall | |
| Wirtschaft ► Betriebswirtschaft / Management ► Wirtschaftsinformatik | |
| ISBN-10 | 1-59749-215-9 / 1597492159 |
| ISBN-13 | 978-1-59749-215-7 / 9781597492157 |
| Zustand | Neuware |
| Haben Sie eine Frage zum Produkt? |
aus dem Bereich