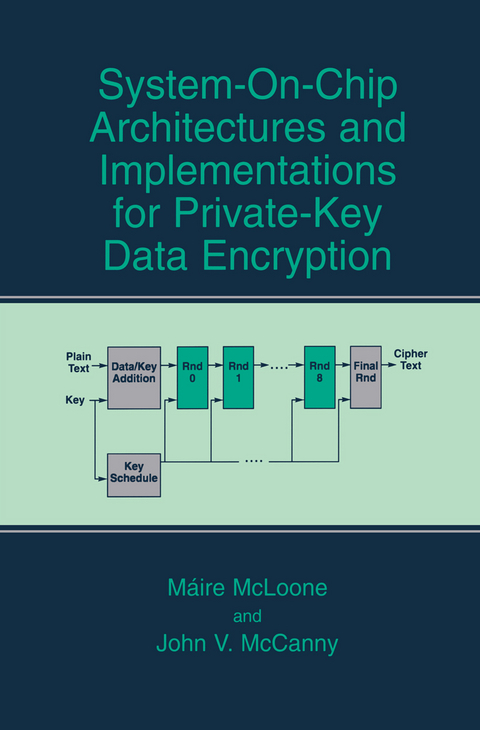
System-on-Chip Architectures and Implementations for Private-Key Data Encryption
Springer-Verlag New York Inc.
978-1-4613-4897-9 (ISBN)
In the opinion of the authors, highly efficient hardware implementations of cryptographic algorithms are provided in this book. However, these are not hard-fast solutions. The aim of the book is to provide an excellent guide to the design and development process involved in the translation from encryption algorithm to silicon chip implementation.
1 Background Theory.- 1.1. Introduction.- 1.2. Cryptographic Algorithms.- 1.3. Cryptanalysis.- 1.4. Hardware-Based Cryptographic Implementation.- 1.5. AES Development Effort.- 1.6. Rijndael Algorithm Finite Field Mathematics.- 1.7. Conclusions.- 2 Des Algorithm Architectures and Implementations.- 2.1. Introduction.- 2.2. DES Algorithm Description.- 2.3. DES Modes of Operation.- 2.4. Triple-DES.- 2.5. Review of Previous Work.- 2.6. Generic Parameterisable DES IP Architecture Design.- 2.7. Novel Key Scheduling Method.- 2.8. Conclusions.- 3 Rijndael Architectures and Implementations.- 3.1. Introduction.- 3.2. Rijndael Algorithm Description.- 3.3. Review of Rijndael Hardware Implementations.- 3.4. Design of High Speed Rijndael Encryptor Core.- 3.5. Encryptor/Decryptor Core.- 3.6. Performance Results.- 3.7. Conclusions.- 4 Further Rijndael Algorithm Architectures and Implementations.- 4.1. Introduction.- 4.2. Look-Up Table Based Rijndael Architecture.- 4.3. Rijndael Modes of Operation.- 4.4. Overall Generic AES Architecture.- 4.5. Conclusions.- 5 Hash Algorithms and Security Applications.- 5.1. Introduction.- 5.2. Internet Protocol Security (IPSec).- 5.3. IPSec Authentication Algorithms.- 5.4. IPSec Cryptographic Processor Design.- 5.5. Performance Results.- 5.6. IPSec Cryptographic Processor Use in Other Applications.- 5.7. SHA-384/SHA-512 Processor.- 5.8. Conclusions.- 6 Concluding Summary and Future Work.- 6.1. Concluding Summary.- 6.2. Future work.- Appendix A - Modulo Arithmetic.- Appendix B - DES Algorithm Permutations and S-Boxes.- Appendix C - LUTs Utilised in Rijndael Algorithm.- Appendix D - LUTs in LUT-Based Rijndael Architecture.- Appendix E - SHA-384/SHA-512 Constants.- References.
| Zusatzinfo | XIV, 160 p. |
|---|---|
| Verlagsort | New York, NY |
| Sprache | englisch |
| Maße | 155 x 235 mm |
| Themenwelt | Informatik ► Theorie / Studium ► Algorithmen |
| Informatik ► Theorie / Studium ► Kryptologie | |
| Technik ► Elektrotechnik / Energietechnik | |
| ISBN-10 | 1-4613-4897-8 / 1461348978 |
| ISBN-13 | 978-1-4613-4897-9 / 9781461348979 |
| Zustand | Neuware |
| Haben Sie eine Frage zum Produkt? |
aus dem Bereich